The High-Rise Heart Attack
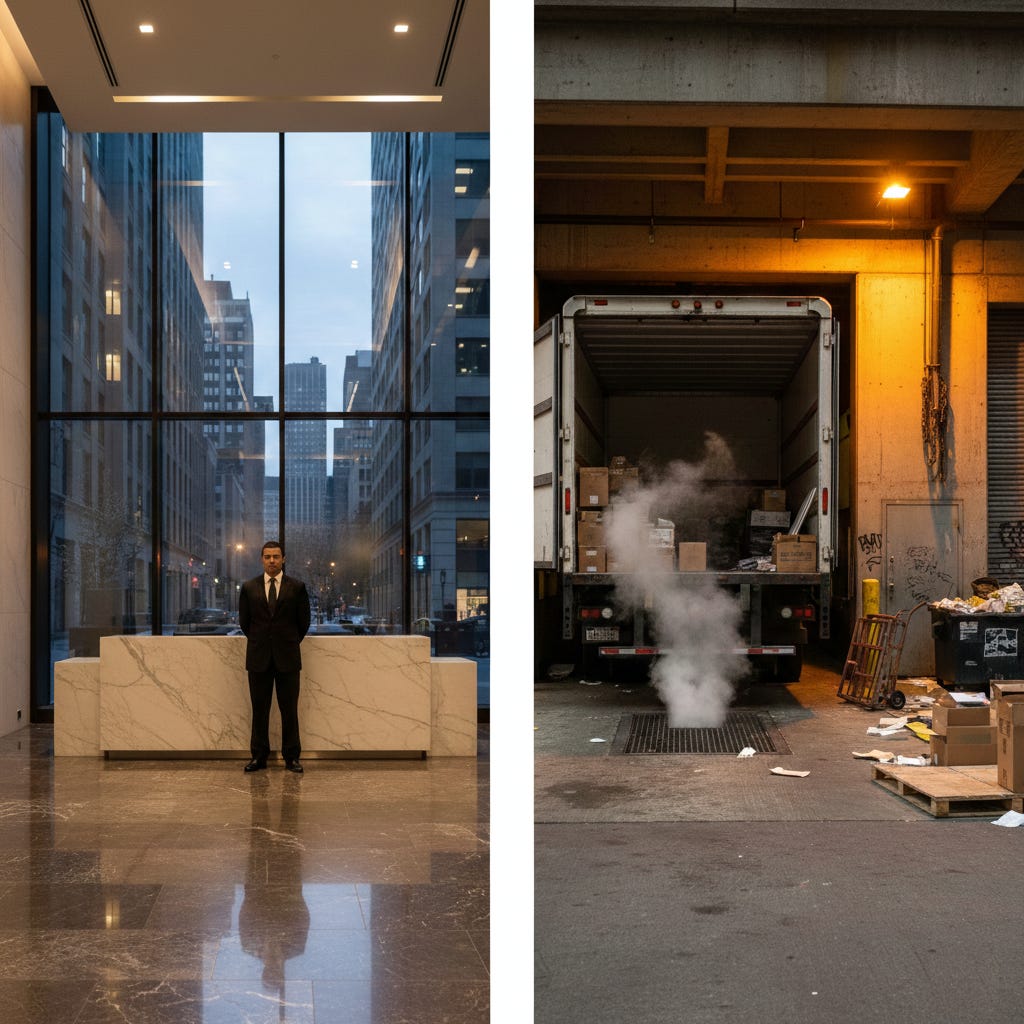
The busiest door in the building is the easiest one to walk through.
THE COUNTERMEASURE
Dispatch #015
If you want to breach a high-security facility, you could spend weeks trying to clone an executive’s badge or bypass a biometric scanner at the front desk. Or, you could just walk around the back to the loading dock between 7:00 AM and 9:00 AM.
In the world of physical security, the loading dock is known as the “Soft Underbelly.” It is the chaotic, noisy, and high-pressure junction where the digital world of the corporation meets the messy, physical world of logistics.
To a hacker like Niko Webb, the loading dock isn’t just a place where trucks park; it’s a security failure waiting to happen.
The Tradecraft: Chaos as Cover
Security thrives on order. At the front desk, one person enters at a time, their ID is checked, and their face is captured by a high-res camera. It’s quiet and controlled.
The loading dock is the opposite. It’s a storm of pallet jacks, beeping trucks, shouting drivers, and stacks of cardboard.
The Vulnerability: Security guards at loading docks are usually overwhelmed. Their job isn’t to check IDs; it’s to manage the flow of goods. They are looking at manifestos, not faces.
The “Clip-In”: Niko puts on a high-vis vest, grabs a ruggedized tablet, and walks in behind a delivery driver. If he looks like he’s annoyed and in a hurry to find a “missing shipment,” he becomes part of the chaos.
The “Crazy” Part: The Trash Compactor Bypass
Here is the secret most people never realize: The trash has to leave.
Almost every major building has a centralized trash room and a massive compactor. These are often located in an area with lower security because, well, it’s trash.
The Flaw: Trash rooms often have their own dedicated exterior doors or chutes that bypass the main security checkpoints.
The Attack: Hackers identify that the “secure” perimeter of a bank vault that actually shares a wall with the building’s waste management area. Why? Because the architects didn’t think anyone would want to hang out in a room full of rotting garbage long enough to drill through a wall.
Niko doesn’t mind the smell. He knows that if you follow the trash, you find the service corridors, and service corridors lead everywhere.
The Logic of the “Invisible City”
The loading dock is the ultimate example of Operational Necessity vs. Security. A building that can’t receive mail or ship products is a building that isn’t working. Because the business must move, security is often relaxed “just for a second” to let a truck in or a delivery through.
Niko Webb lives in those “seconds.” He knows that the most expensive security system in the world can be defeated by a guy with a clipboard and a convincing “I’m late for a delivery” scowl.
Note to readers: my book featuring white hat hacker Niko Webb is out now on Amazon! Read the first chapter for free on Substack.
The Sign-off
This concludes our tour of The Invisible City. I hope you’ll never look at an elevator keyhole, a manhole cover, or a ventilation duct the same way again. The world is a lot more connected (and a lot more vulnerable) than it appears on the surface.
Next week, we’re shifting gears. We’re going to talk about The 60-Second WiFi Crack. I’ll show you exactly how Niko captures your home network’s “handshake” from the sidewalk and why your password probably isn’t enough to stop him.
Stay dangerous,
Alex Holt